
Top 10 IT Issues, 2022: The Higher Education We Deserve

AI vs. Human Is a False Choice

Cyber Attack Survival Manual: From Identity Theft to The Digital
Authenticate This LV: READ the rules & use the format in post #1
What is a Security Policy? Definition, Elements, and Examples
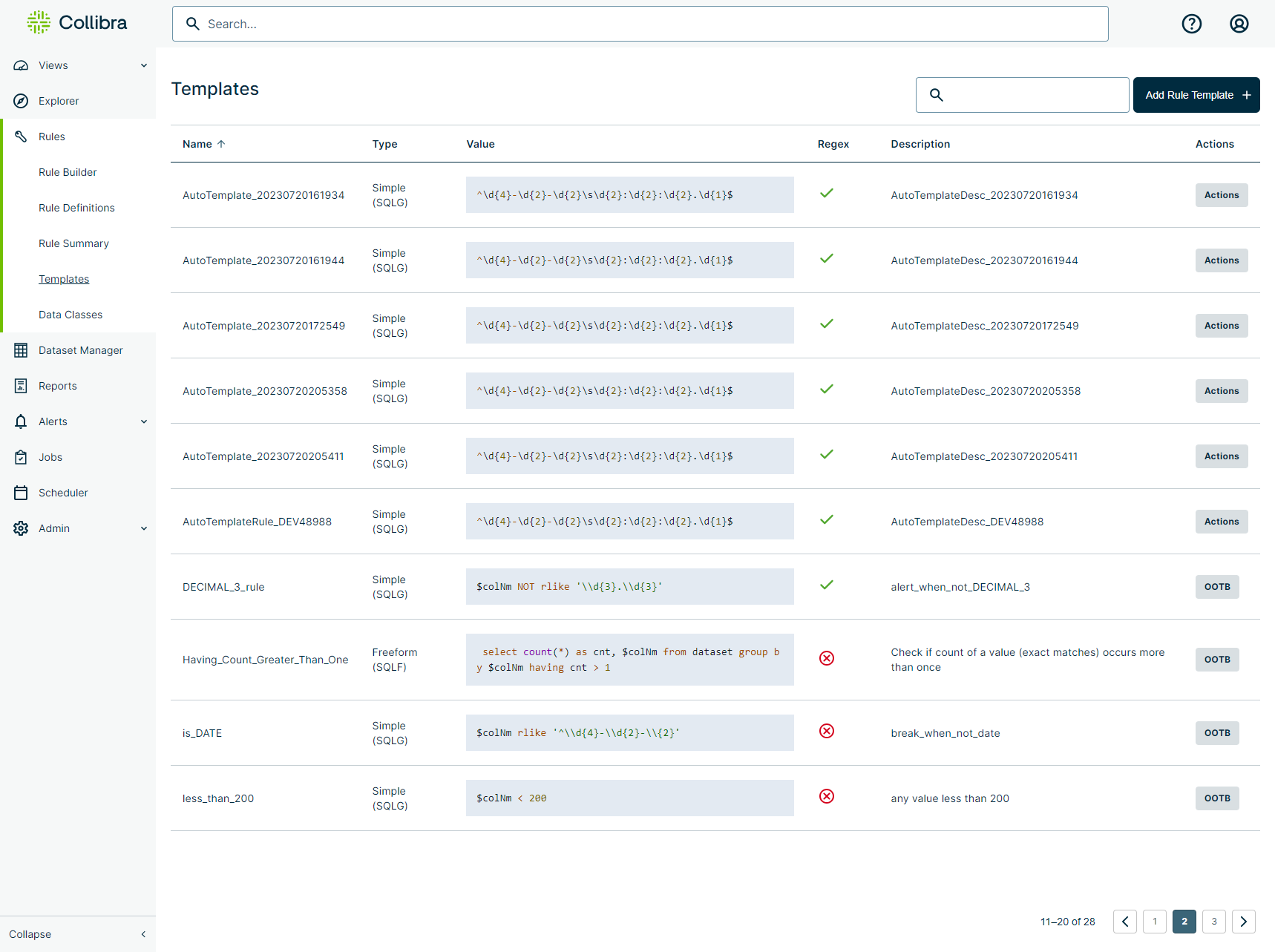
Templates

Island's Enterprise Browser Blog

An algorithm for quality - by Chris Best - On Substack
New ways to customize your Substack - On Substack

Wiz Research discovers ExtraReplica— a cross-account database

SolarWinds breach: The next level of stealth
Documentation

5 Essential Tips for Writing Secure Firestore Security Rules
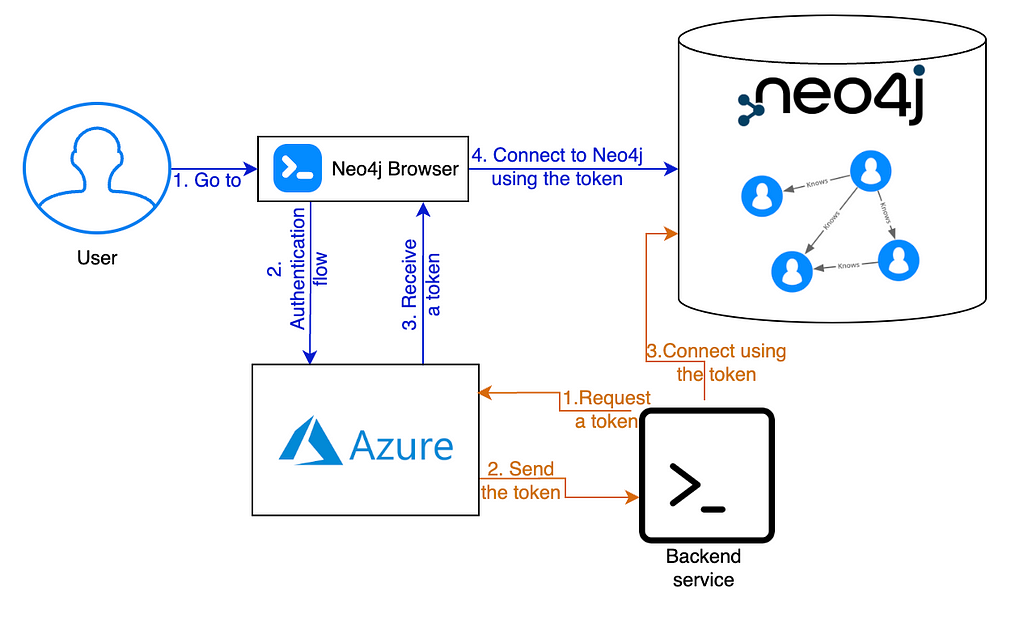
How to Integrate Neo4j With SSO on Azure: One Login to Rule Them
