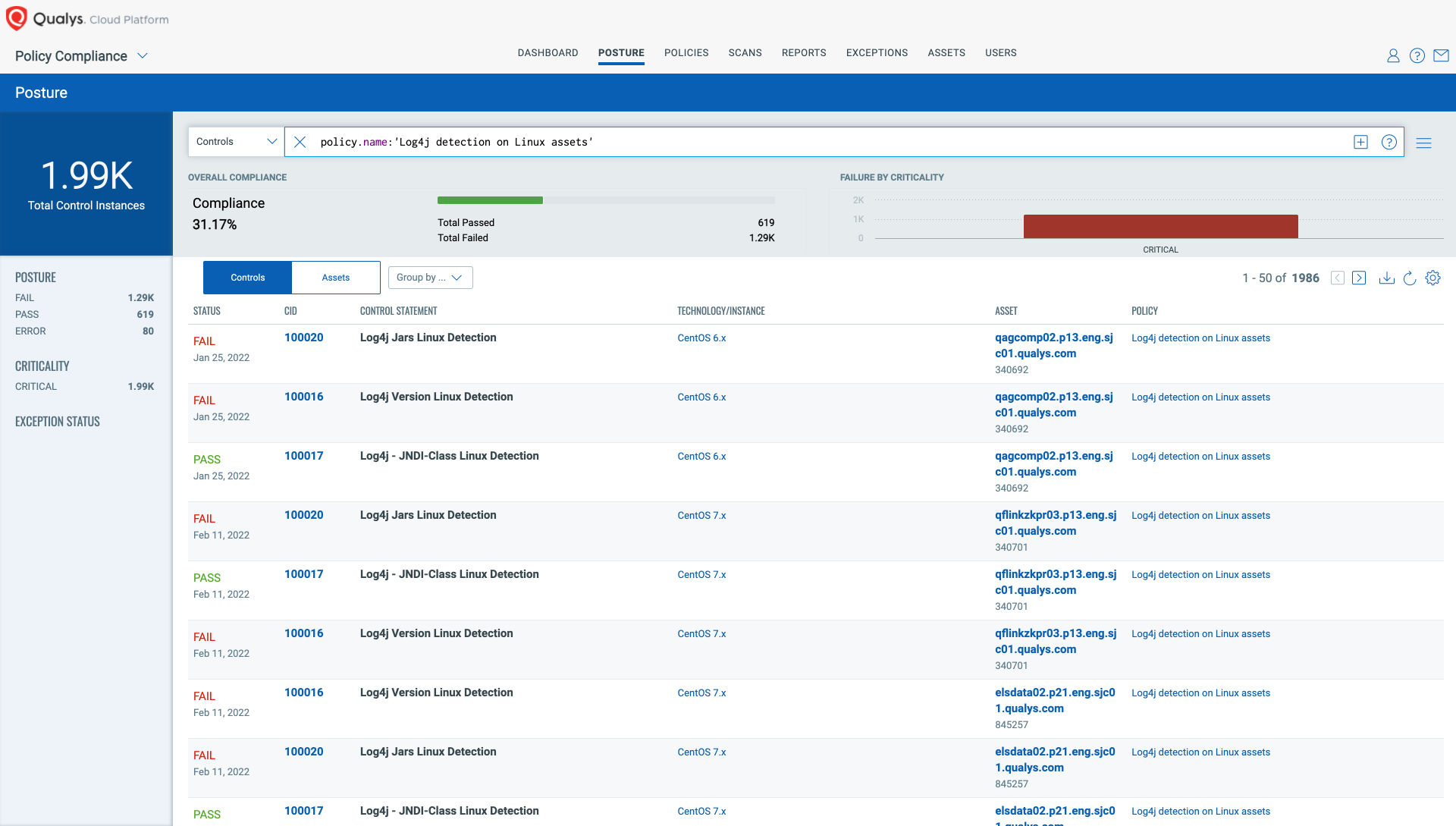
What's Next After Log4Shell? - vulnerability database
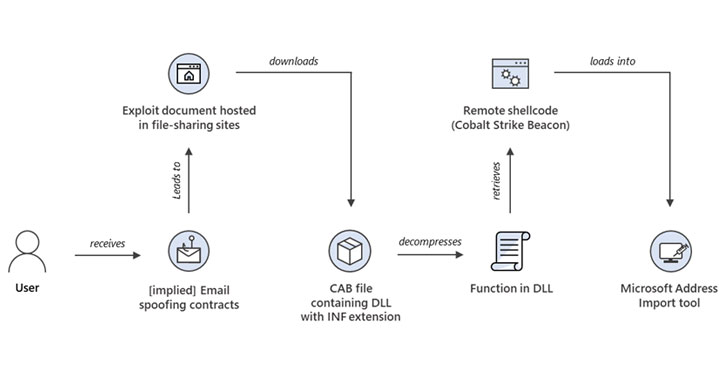
Windows MSHTML 0-Day Exploited to Deploy Cobalt Strike Beaco - vulnerability database

Stolen Treasures—And the Lucrative Black Market That Spans the Globe - Mangoprism
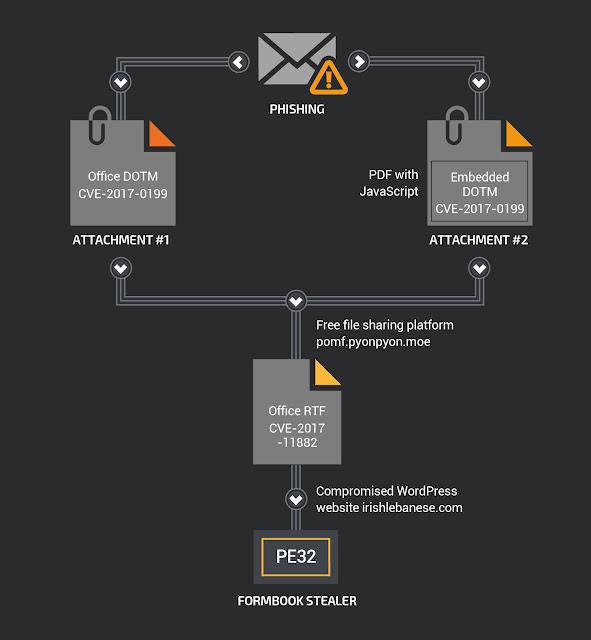
My Little FormBook - vulnerability database

The unknown actual state of artist's work of how artworks how to create wealth in a fake - GIGAZINE
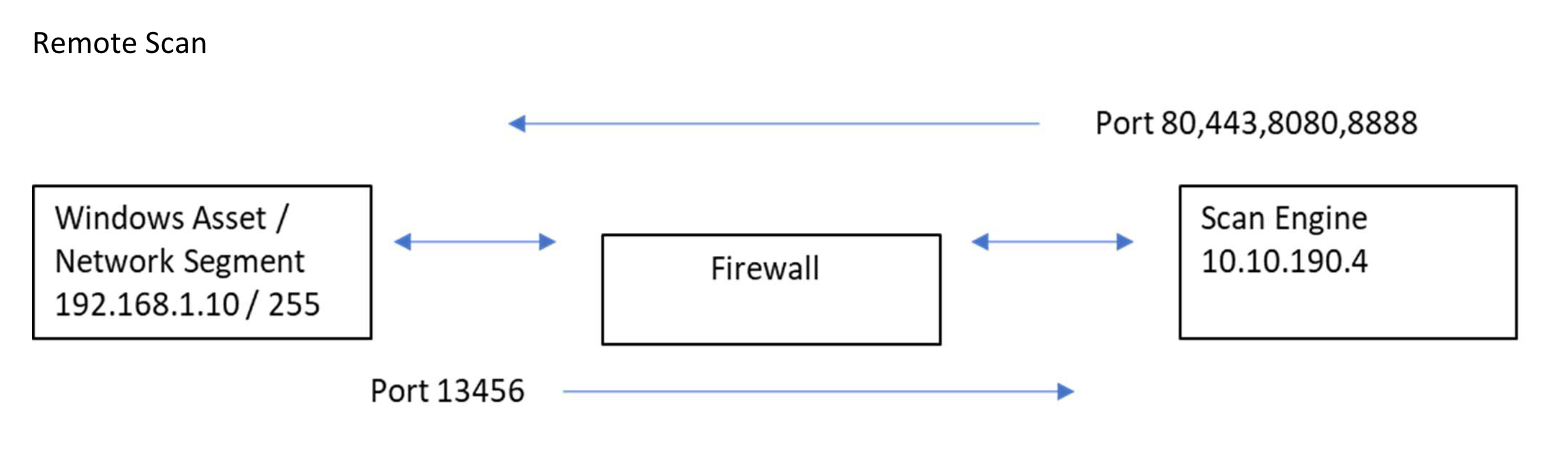
Using InsightVM to Find Apache Log4j CVE-2021-44228 - vulnerability database

The Vast Majority of Antiquities Sold Online Are Probably Looted or Fake, a New Report Says

QSaltLake Magazine - 298 - April 18, 2019 by QSaltLake Magazine - Issuu
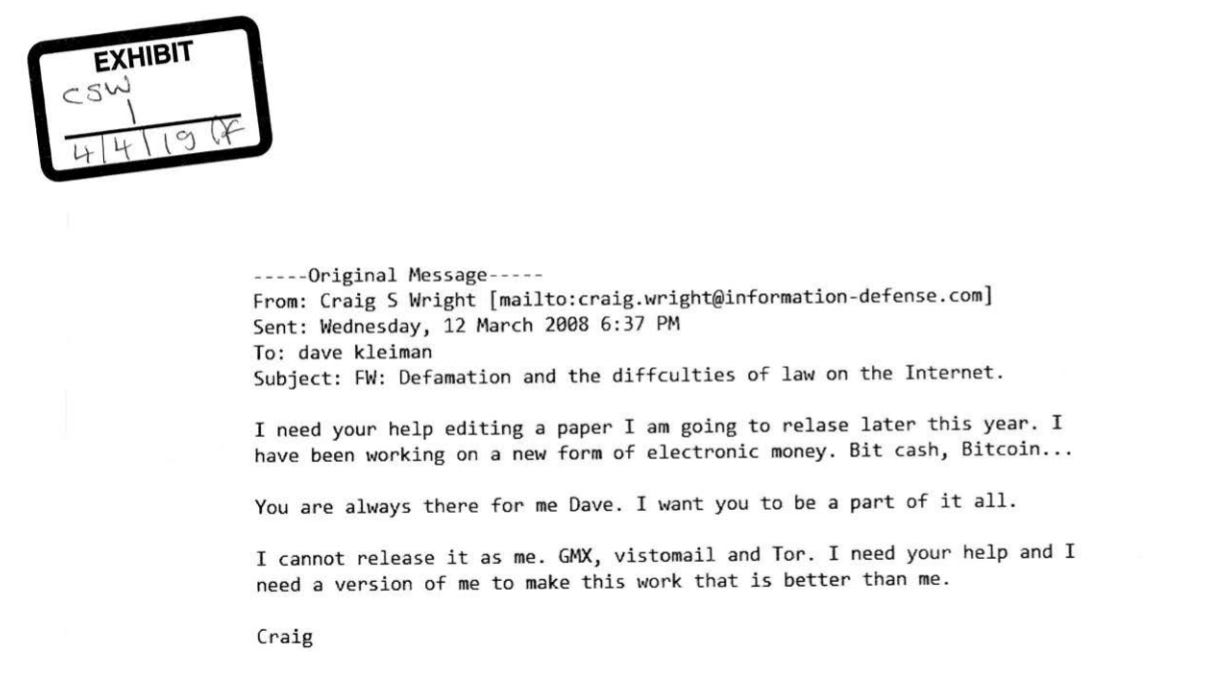
Faketoshi, The Early Years — Part 1, by MyLegacyKit

Branded Earbud Detail Kit – Pinch Provisions
sideng-1/kkaa at master · simdj/sideng-1 · GitHub
TVO Original “There Are No Fakes” reveals a dark tale of

Malware Posing as Russia DDoS Tool Bites Pro-Ukraine Hackers - vulnerability database
