
Microsoft Office Vulnerabilities Used to Distribute FELIXROO - vulnerability database
cookbook-2nd-data/troll.csv at master · ipython-books/cookbook-2nd-data · GitHub

LOUIS VUITTON BAG SIZE GUIDE - BB vs PM vs MM vs GM - MISLUX
PHP-Rake-IDF/idf.json at master · scrivna/PHP-Rake-IDF · GitHub

Goyard Artois (PM, MM & GM) - Complete Guide and Review 2023 - Luxe Front
Insults/Insults/Data/Inputs/train.csv at master · cbrew/Insults · GitHub
Louis Vuitton Portobello Bag Reference Guide - Spotted Fashion
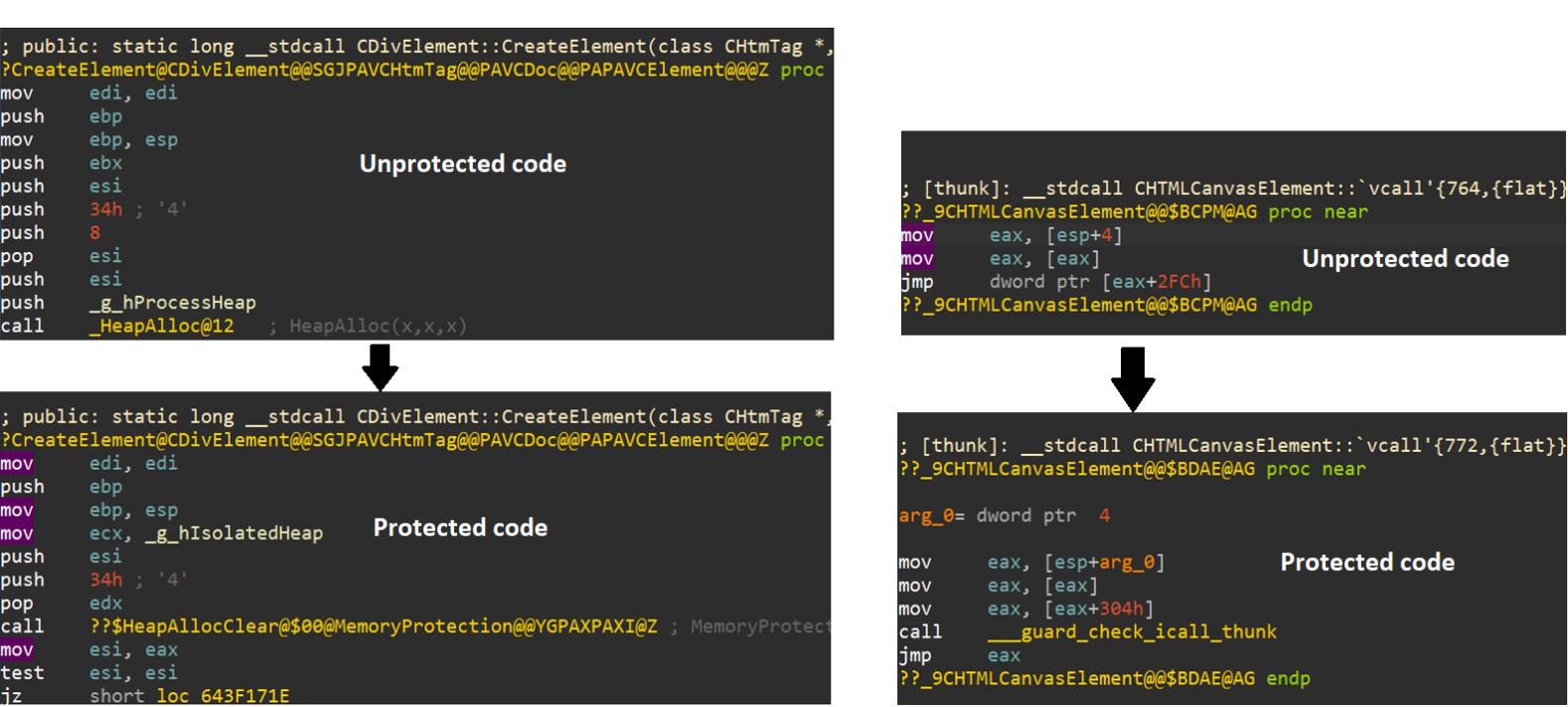
Beyond Memory Corruption Vulnerabilities – A Security Extinc - vulnerability database

LOUIS VUITTON AGENDA COMPARISON, GM vs. MM vs. PM

My 2020 Agenda Setup Louis Vuitton Monogram MM - The Luxe Minimalist Louis vuitton planner, Louis vuitton agenda, Louis vuitton monogram

quacs-data/faculty.json at master · quacs/quacs-data · GitHub
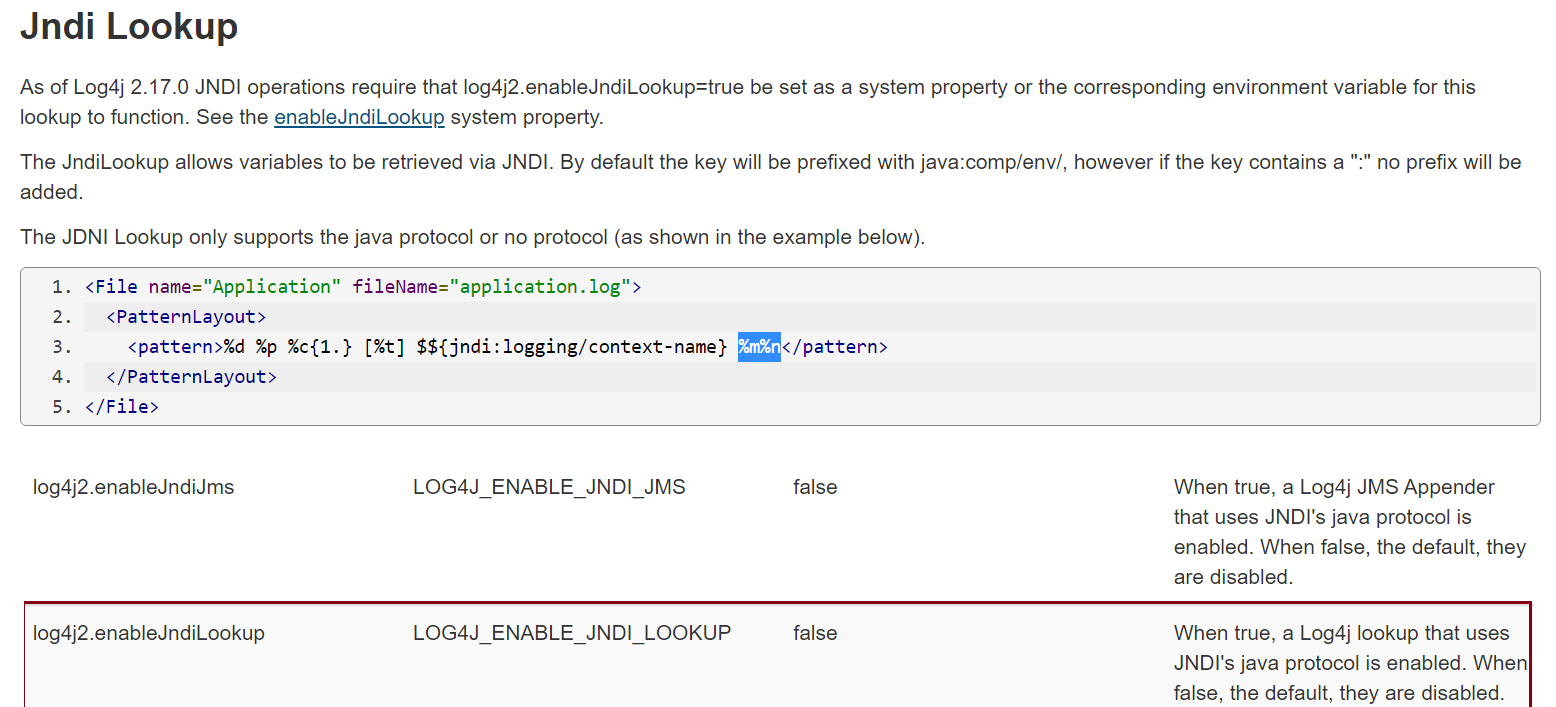
Beyond Memory Corruption Vulnerabilities – A Security Extinc - vulnerability database
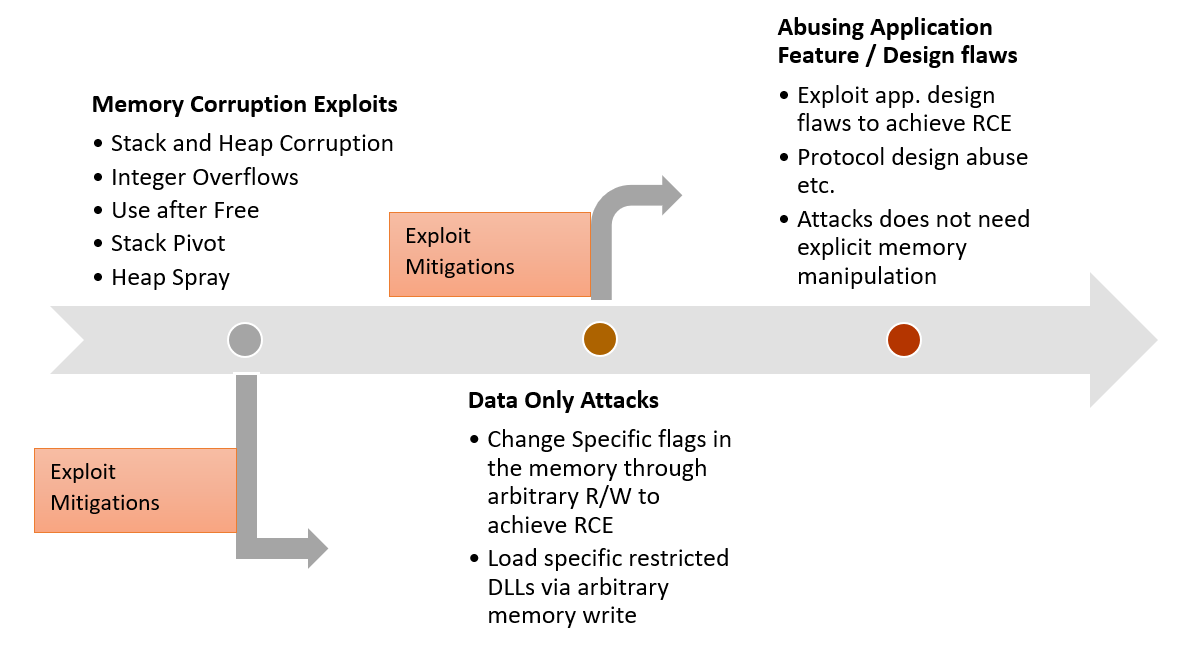
Beyond Memory Corruption Vulnerabilities – A Security Extinc - vulnerability database
